Zero Trust has emerged in the past ten years as the foundational approach to cybersecurity for many organizations. As the name implies, Zero Trust is about removing the presumption of trust for all users, i.e. “never trust, always verify”. Instead of a one-time access decision, trust is continuously addressed and evaluated, and access is limited to least privilege.
While the Zero Trust concept is fairly mature, its application to IoT and unmanaged devices is relatively new, but growing.
New research from EMA points to IoT as one of the top drivers for enterprise interest and investment in zero-trust networking (46% of enterprises).
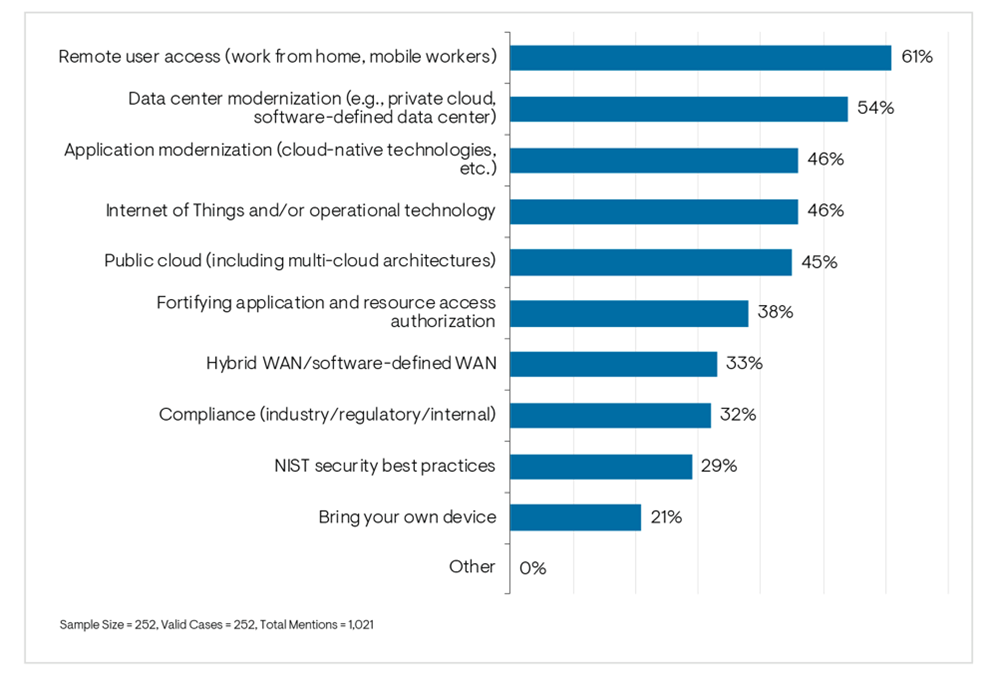
The EMA report, “Enterprise Zero Trust Networking Strategies: Secure Remote Access and Network Segmentation” based on a survey of 252 enterprise technology professionals, discovered the following:
- IoT drove healthcare, manufacturing, and professional IT services companies towards Zero Trust networking, while software and retail companies were the least influenced by IoT.
- IoT and other unmanaged devices present a challenge to Zero Trust networking policy design because they have no users associated with them and require an alternative way to authenticate connection requests. 38% of enterprises surveyed create tailored access privileges based on the functions and characteristics of individual devices or classes of devices. This means that 64% of enterprises establish generic access for all devices or devices are untrusted with limited access, or are untrusted and banned from the corporate network.
- Establishing a generic, minimum level of access privilege for IoT and unmanaged devices, such as an IoT VLAN, is popular among government agencies (50%) and healthcare organizations (55%). However, this strategy isn’t ideal as risks can differ even among a set of similar IoT devices based on behavior, vulnerabilities, manufacturer.
- The most important parameters for determining access privileges of unmanaged devices were cited as security status, device vulnerability and risks, owner of the device, and observed network behavior. This makes sense so that enterprises can use tailored policies and place devices in the right “trusted” areas of the environment.
- Enterprises are more likely to succeed with tailored policies for unmanaged devices if they formed a Zero Trust networking taskforce rather than relying on formal partnerships between network and security teams.
- Identifying and segregating IoT and other unmanaged devices is a top priority for healthcare organizations (55%). This is not a big surprise given the vast numbers of sensors, scanners, and other medical equipment that connect to networks in clinics, hospitals, and laboratories.
- The top issue that enterprises find most challenging to Zero Trust network segmentation are the high volume of changes and exceptions straining management capacity. This points to a need for network automation.
- 92% of enterprises want tools that simplify segmentation, specifically to address “exceptions/custom rules”, cross-tool support, and to automate/eliminate errors — this is especially true for IoT since there are so many different types of devices and their numbers are so large that automation is critical to drive Zero Trust segmentation
As the report shows, enterprises are recognizing the need to extend Zero Trust to unmanaged and IoT devices. 50% of enterprises in the EMA survey have started Zero Trust microsegmentation in the LAN where IoT lives. To do this effectively and without manual errors, automation is critical. Ordr can help. We help enterprises discover and profile devices so they know exactly what an IoT device is at a very granular level, how it is behaving, and protect these devices at the firewall and in the network via automated Zero Trust and microsegmentation policies.
We invite you to download the report summary here. For complete visibility into what’s in your network, sign up for our IoT Discovery Program at www.ordr.net/sensor.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud