I am excited to announce the integration of Ordr Systems Control Engine (SCE) and VMware NSX-T™ Data Center and VMware NSX® Intelligence™.
Ordr Systems Control Engine (SCE): Discovers every connected device, profiles device behaviors and risks, and automates response. Ordr not only identifies devices with vulnerabilities, weak ciphers, weak certificates, and active threats, but also those that exhibit malicious or suspicious behaviors. Ordr enables networking and security teams to easily automate response by dynamically creating policies that isolate mission-critical devices, those that share protected organizationally unique sensitive data (PCI, PHI, PII) or run vulnerable operating systems.
VMware NSX-T Data Center: Includes Distributed Firewall functionality to specify dynamic security policies down to the VM level with the ability to configure east-west and north-south firewalling.
VMware NSX Intelligence: Provides a graphical user interface to visualize the security posture and network traffic flows that have occurred in your on-premises NSX-T Data Center environment.
With the integration, joint customers can now:
- Achieve cutting edge visibility
- Accelerate NSX-T Data Center microsegmentation
- Minimize the potential business impact associated with firewall changes
If your VMware NSX data center firewall microsegmentation team is looking for a method to significantly reduce the overhead of maintaining static NSX-T IPsets and group objects, it is time to consider a solution that is capable of addressing the following scenarios:
- Automated NSX-T group object creation for non-data center device types
Since NSX-T provides excellent visibility for the entire data center, the most time-consuming objects to create and maintain are ones which pertain to devices outside of the data center (enterprise campus, branch sites, etc).
Ordr continuously discovers devices as they join campus and branch networks and can automate the creation of corresponding group objects in NSX.
NOTE: Ordr creates NSX objects with a standard prefix of “ordr-“. This allows NSX admins to easily recognize which objects are autogenerated and maintained by Ordr.
- Automated IP address membership tracking for NSX group objects
Dynamically creating NSX-T groups is a great start, but this capability alone does not solve the labor-intensive aspect of maintaining IP address membership for each type of device.
Ordr tracks the IP addresses of each type of device in the campus and branch. If a credit card reader device IP changes, Ordr will automatically update the NSX group with the new IP address. - Support for advanced visualizations in the latest version of NSX Intelligence
Ordr programmatically creates NSX group objects and their members in a format which is compatible with the latest version of NSX Intelligence (announced at VMworld 2020[CI1] ).
This means that NSX Intelligence is able to render all communications from Ordr-defined and maintained NSX device groups.
This capability is key for teams who are looking to accelerate their data center security initiatives by gaining a comprehensive understanding regarding all types of campus and branch devices which are communicating to virtual machines in the data center.
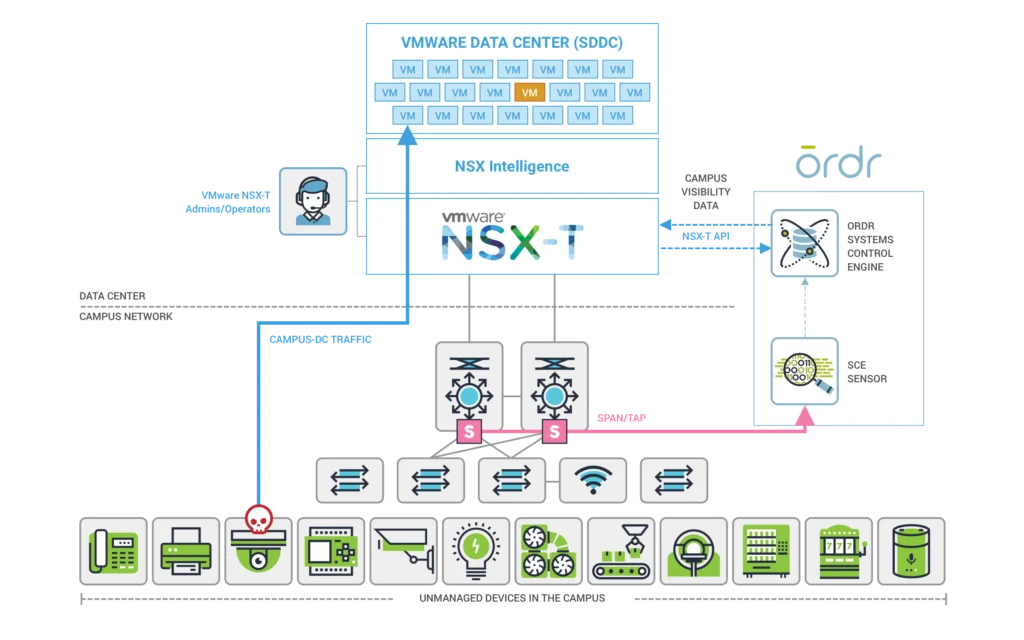
How it works:
Step 1
Ordr SCE sensors use advanced deep packet inspection (DPI) techniques to process campus and branch traffic from a SPAN/port mirror, TAP, or packet broker feed
Step 2
Ordr SCE sensors forward metadata to the SCE Analytics system which identifies all the device types (including unmanaged IoT devices) which are communicating on the campus network
Step 3
Ordr SCE Analytics programmatically creates NSX groups and their member IP addresses
NSX Intelligence with Ordr device data in action:
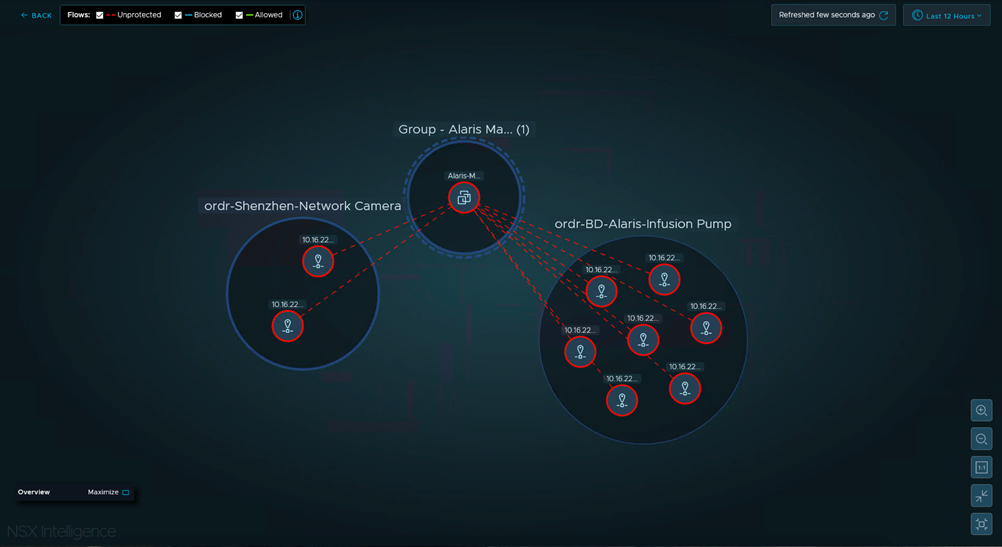
In this example screenshot from NSX Intelligence, we can quickly see that the Alaris Manager VM is receiving unprotected communication from two different device types in the campus network.
NSX group 1: ordr-BD-Alaris-Infusion-Pump
NSX group 2: ordr-Shenzhen-Network-Camera
This type of information can be leveraged to reduce the amount of manual labor associated with understanding source/destination communication for thousands of different campus and branch device types communicating to virtual machines in the data center.
In summary, the Ordr integration with NSX-T Data Center and NSX Intelligence allows teams to achieve greater operational efficiency by automating labor intensive tasks and unlocking rich device type context visibility for all campus and branch devices communicating with virtual machines.
For more on how one of our customers is leveraging this integration today, visit our on-demand VMworld breakout session NSX Intelligence: Visibility and Security for the Modern Data Center – Pt2 [ISNS2496] with Ray Budavari, Sr. Staff Technical Product Manager at VMware, Brandon Rivera, Enterprise Infrastructure Architect at CHRISTUS Health, and myself as we take a deep dive into the integration, and provide a demo of the Ordr and NSX Intelligence capabilities.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud